Computer Forensics
Get our digital forensic experts to uncover the answers you need!

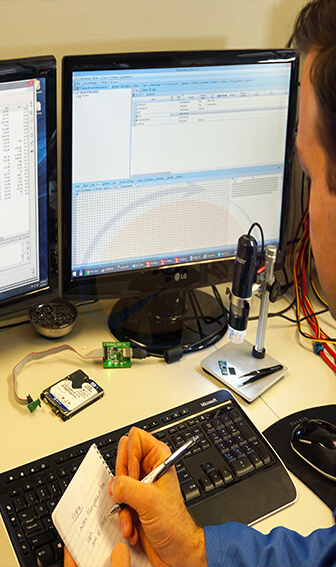
When computers are used, many sensitive pieces of information and metadata are stored in the background by apps and the operating system. Data that is hidden, buried in system folders, and might hold important information, are called digital artifacts. Our computer forensic analysts use industry leading tools, like EnCase and PC3000, to seek the digital artifacts needed to answer questions central to your important case.
User passwords and domain security are usually no hindrance when it comes to extracting data from storage devices. Even if the drive has been recently re-formatted or sustained a physical damage, we can use our fully equipped data recovery lab and decades of combined experience to complete a full forensic analysis for any sort of case.Whether your computer is running Windows, Linux, Mac, or a legacy operating system, our digital forensic analysts can scour any computer drive to extract important information. Operating system logs, setting files, auto-complete lists, and more, are routinely analyzed by our experts so we get the digital evidence pertaining to your case. We then catalogue the relevant digital artifacts for your case, and prepare a forensic analysis report or comprehensive expert opinion. With the information analyzed and meticulously detailed, your case will be strengthened by a better understanding of its digital evidence through competently applied computer forensics.
Types of information computer forensics can extract and analyze from a hard drive include:
Who We Help
Digital forensics can be useful in a wide array of circumstances. Contact us today to find out more about how our experts can assist with your case.
We expertly seek hard-to-find digital artifacts in a court-acceptable manner for your case. No digital evidence is too small for us to analyse and report on. From simple extraction and analysis of deleted email messages, to a complex timeline analysis of system-wide activities, we tailor our services to meet the needs of your case.
It doesn’t have to be a legal case; we understand that some situations will never go to court. Regardless of the circumstances, we will offer a customized service that will answer your important questions to provide peace-of-mind.
It is important that any digital evidence provided in a legal process be expertly extracted and analysed by a professional. If you believe your computer may need digital forensic services, stop using it and discuss the situation with us. Contact us for a free consultation on how we can analyse the digital evidence in your case.
We can forensically address questions about:
- Spying software
- Malware and viruses
- Youth Internet activity
- Infidelity suspicions
- Illegal activities
- Internet Use History
Our digital forensic analysts can acquire hard-to-find information located on NAS, RAID, Drobo, flash drive, and computers used by staff. Many types of commercial crime and corporate misconduct can be analysed expertly to discover incidents like fraud, intellectual property theft, suspicious network communications, employee disloyal activity, deletion of data, improper web activities, email abuse, and exfiltration of company secrets.
We can dispatch an analyst to your place of business to begin on-site digital forensic extractions to preserve information relating to your case with minimal disruption to your business activities. To avoid overwriting digital artifacts, a quick response is best to forensically preserve information relating to your case. Contact us for a free consultation on how our forensic services can help your business’s legal case.
We can forensically address questions about:
- Employee fraud
- Improper use of resources
- Harassment and bullying
- Commercial espionage
- Insider trading
- Acceptable-use policy violations
Engaging us to assist the court in understanding the digital evidence in your case can be crucial in providing the best service to your client and the justice system. We understand the obligation that experts must present digital forensic evidence in a manner that helps the court, rather than advocate for your client. We ensure our reports and testimony will be accepted and heavily weighted by the trier of fact and will avoid the common pitfalls many experts find themselves in when they do not work in the interest of the court, but task themselves with the improper mission of bolstering a client’s case contrary to court rules.
We will work closely with you and your client to search for answers that digital evidence can provide. To determine the best strategy to assist with your unique case, we provide complimentary initial consultations.
The number of digital fingerprints left behind by clients and targets of your investigations constantly grows. Nearly everyone has a device that stores digital artifacts which could make or break an investigation. Putting the extraction and analysis of vast troves of data into the hands of our experts will help you focus on the investigation, while we take care of the digital evidence gathering.
Multiple devices may have data where proper cross-reference will generate new leads. With the tools we have at our disposal, complex analysis, such as combining multiple digital evidence sources, can find connections that would otherwise stay hidden.
Contact us for a free consultation on how we can assist with your investigation.